Who Is Caesar Cipher? What Did He Do? What's The Mystery Behind The Locks? What's The Secret?
Cryptography is the art of keeping secrets, and at its core, it is built on some of the deepest ideas in mathematics. From the humble Caesar cipher to the public-key systems that protect your messages, number theory, modular arithmetic, and algebraic structures do the heavy lifting.
It Started 2,000 Years Ago 🏛️
Julius Caesar — yes, the Roman emperor — invented one of the first encryption methods to communicate with his soldiers without the enemy understanding him. His idea? Shift every letter in the message by three positions. So H becomes K, E becomes H... and "HELLO" quietly becomes "KHOOR".
Reverse the shift and you've got your message back. Simple, elegant — and the direct ancestor of every encryption system protecting your data today.
Lets Dig Deep Together And Solve This Mystery Once And For All
Missed The Seminar? Don't Worry, Watch it here: (Just Don't Miss The Next One)
Math Society Topic: Cybersecurity And Cryptography
RSA And Modern Encryption. Wait What?
One of the most widely used cryptographic systems today is RSA. It works by using two large prime numbers whose product forms a public key. While anyone can encrypt messages using the public key, only the owner of the private key can decrypt them. Think of it as a padlock anyone can close, but only one person holds the key to open.
RSA's security relies on the fact that factoring very large numbers into primes is extremely difficult for classical computers. We're talking primes that are at least 300 digits long — their product becomes a 600-digit number. Go ahead and try to factor that with a for loop. We'll wait.
RSA Threat: RSA encryption relies on the difficulty of factoring very large numbers into their prime components. If factoring becomes efficient, attackers could compute the private key from the public key.
Shor's algorithm: A quantum algorithm designed to factor large numbers efficiently — and the reason the cryptography world is quietly panicking.

Exploring the future of encryption – "Are we cooked?"
Post-quantum cryptography and lattices
Because quantum computing threatens current encryption systems, researchers are developing new cryptographic methods based on different mathematical problems. One promising area is lattice-based cryptography, which uses geometric structures formed by combinations of vectors. Problems such as finding the shortest or closest vector in a lattice are extremely hard, even for quantum computers. So we traded one hard problem for another — this time in geometry.
Learning With Errors (LWE) encryption
A key lattice-based system is the Learning With Errors (LWE) problem. It looks similar to solving linear equations, but includes small random noise that makes recovering the secret solution computationally difficult. This randomness ensures that encrypted messages cannot be distinguished from random data, providing strong security. LWE and related methods are considered leading candidates for future quantum-resistant cryptography.
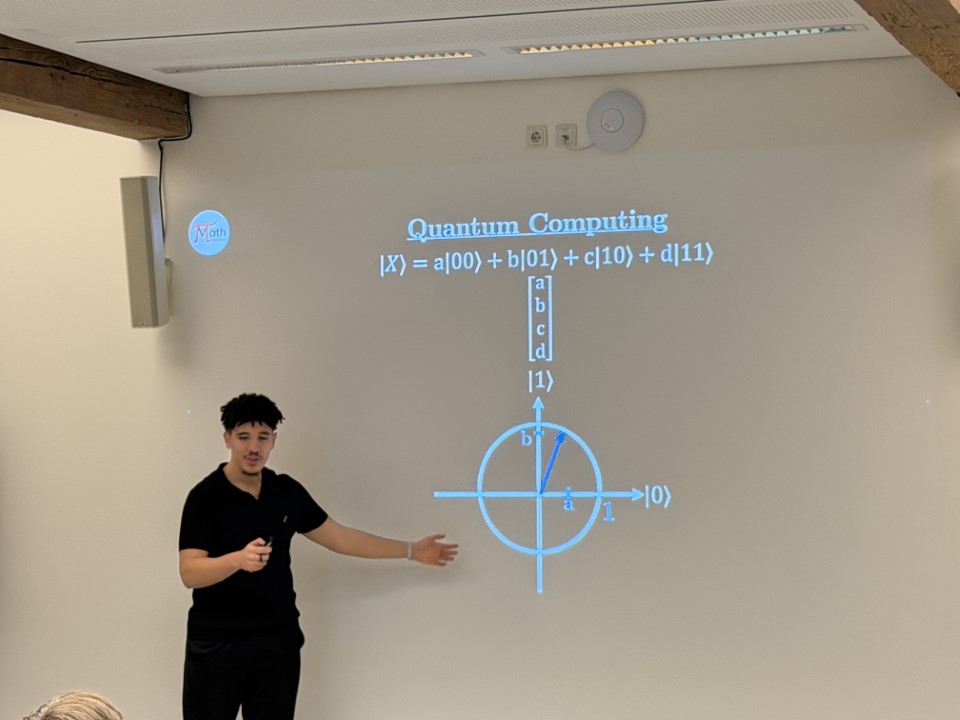
Explaining quantum states and superposition during the seminar.
Conclusion
Modern cryptography is built on mathematical problems that are difficult for classical computers to solve, with RSA standing as one of the most important examples. However, the development of quantum computing introduces a fundamental shift in computational power. Through Shor's algorithm, quantum computers could efficiently factor large numbers, threatening the security assumptions that protect today's digital communication. This challenge has motivated the search for new cryptographic systems, such as lattice-based methods, designed to remain secure even in a quantum era. Ultimately, the future of cybersecurity depends on adapting mathematical tools to evolving technology, showing that advances in mathematics and computing continuously reshape how we protect information.
So — are we cooked? Not yet. But the clock is ticking, and mathematics is already working on the answer.